In-app advertising has never been more popular. Advertisers appreciate the targeted traffic that makes their campaigns effective, while app publishers value the fact that they can grow an audience and monetize without charging a premium price. But there is a downside to the massive growth of in-app advertising. Fraudsters are incentivized to try gaming the system with invalid traffic.
High-quality traffic is what makes in-app advertising so popular. It’s what turns advertising campaigns into a success and allows publishers to earn revenues. While high-quality traffic is the lifeblood of mobile advertising, invalid traffic is a risk. Invalid traffic is traffic generated by non-human sources that can make advertising campaigns look more successful than they actually are. However, not all invalid traffic is necessarily fraud.
It’s important to know the differences in the types of invalid traffic, so let’s take a look at the difference in the two wildly different types of invalid traffic: general invalid traffic (GIVT) and sophisticated invalid traffic (SIVT). All of the following information comes from our new whitepaper, Understanding In-App Advertising Fraud. This guide to combating fraud in programmatic advertising looks at the different types of fraud and the methods used to fight that fraud.
What Is General Invalid Traffic (GIVT)?
GIVT is the least harmful form of invalid traffic. This traffic comes from crawlers and bots from benign sources. Examples include data centers, search engine crawlers, or proxy traffic coming through a virtual private network (VPN). This traffic doesn’t attempt to mimic human behavior. Therefore, GIVT isn’t considered fraud.

What Is Sophisticated Invalid Traffic (SIVT)?
SIVT is outright fraudulent traffic that tries to appear legitimate. This traffic avoids the simple patterns of GIVT and can be a serious threat to traffic quality. Detection is not always easy, and the methods used by fraudsters to create SIVT are becoming increasingly sophisticated.
- Adware/malware: Harmful software installed on legitimate devices can generate illicit traffic without the user’s knowledge or consent.
- Bots: These are designed to behave like real human users to trick advertisers into paying for an audience that doesn’t actually exist.
- Concealed/Stacked ads: Several ads stacked on top of each other end up misleading advertisers. While only the top ad is visible, all the advertisers pay for what they think are viewable ads.
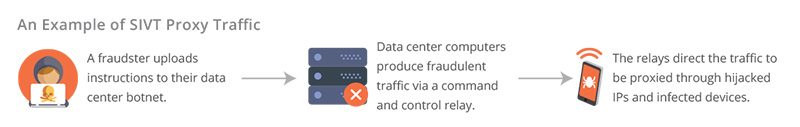
- Fraudulent proxy traffic: Although many actual users generate proxy traffic (through VPNs, for example), fraudulent proxy traffic is often used to mask bot traffic.
Fraudsters often use a combination of different methods in an attempt to evade detection. In one of the more prominent cases of SIVT in the mobile advertising industry, fraudsters purchased legitimate, popular apps to attempt their scheme. These fraudsters then mixed the actual human traffic with sophisticated bots, making it harder to detect. There was a whole network of these apps, and the bid request information was falsified using a fraud tactic called “spoofing.” Lower-quality apps represent themselves as more premium apps.
How to Limit Sophisticated Invalid Traffic
SIVT is tricky because it’s designed to look like legitimate, valid traffic. However, it is possible to identify and end this form of fraud when it happens. A combination of advanced analytics and expert human intervention can significantly mitigate the impact of SIVT. Most importantly, it’s critical to work with partners who are serious about creating a protected mobile marketplace. Learn more about Smaato’s market quality initiatives here: https://www.smaato.com/resources/market-quality/.




